
The global energy landscape is undergoing a fundamental transformation. As nations race toward decarbonization targets and grid modernization, Battery Energy Storage Systems (BESS) have emerged as critical infrastructure components, bridging the gap between intermittent renewable generation and reliable power delivery. The International Energy Agency projects that global battery storage capacity will need to increase exponentially - from approximately 200 GW today to over 1,500 GW by 2030 - to support the energy transition.
However, tis rapid proliferation of distributed energy resources introduces a cybersecurity challenge that fundamentally differs from anything the energy sector has faced before. Unlike traditional centralized power infrastructure with its limited attack surface and well-understood threat models, BESS installations create a vast, geographically dispersed ecosystem of interconnected systems. Each installation represents not just a potential point of failure, but a possible attack vector that could cascade into grid-wide disruptions.
For CISOs in the energy sector, this represents both a challenge and an opportunity. The challenge is evident: protecting distributed assets with complex operational technology, legacy protocols, and safety-critical systems. The opportunity lies in recognizing that robust cybersecurity isn't merely a compliance requirement - it's an enabler of the energy transition itself, creating stakeholder confidence, enabling market participation, and ensuring operational resilience.
The Expanding BESS Deployment Landscape
BESS installations span multiple deployment contexts, each with distinct operational requirements and security implications.
Utility-Scale Grid Storage: Multi-megawatt installations providing frequency regulation, peak shaving, and renewable energy integration services directly to transmission operators.
Commercial & Industrial Sites: Behind-the-meter systems optimizing energy costs and providing backup power for critical facilities - from data centers to manufacturing plants.
Residential Systems: Growing deployment of home battery systems coupled with rooftop solar, creating millions of potential grid endpoints.
Remote & Microgrid Applications: Isolated BESS installations supporting mining operations, island communities, and military bases where grid resilience is mission-critical.
This distributed architecture fundamentally changes the threat model that energy sector CISOs must address. Where traditional power infrastructure featured centralized generation with limited external connectivity and well-defined security perimeters, modern BESS deployments require constant communication with grid operators, energy management systems, remote monitoring platforms, and market participants.
The attack surface has expanded from a few highly-secured central facilities to potentially thousands of distributed points of presence, each requiring protection while maintaining operational flexibility and economic viability.
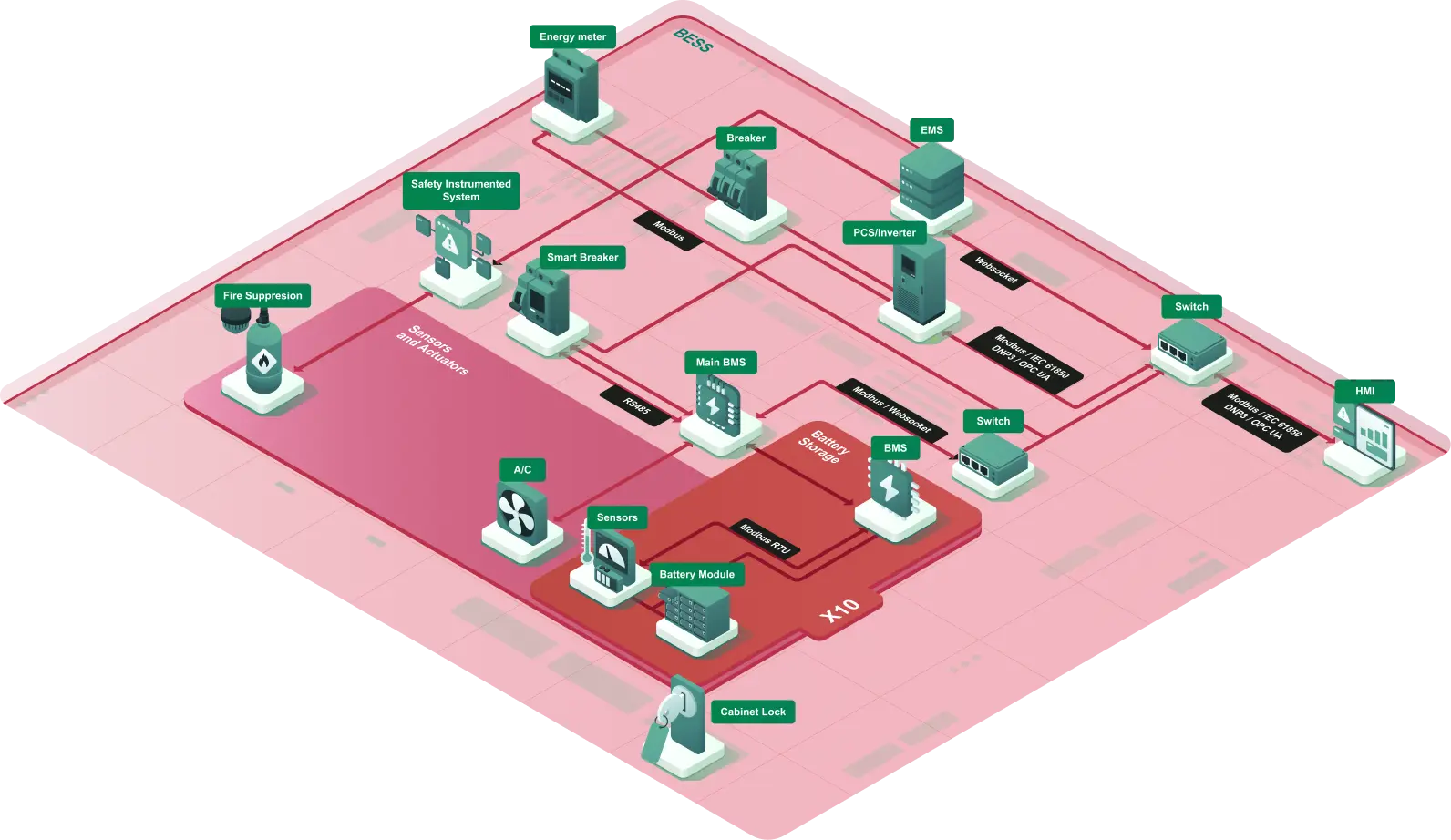
Mapping the Attack Surface: A Comprehensive Threat Analysis
The attack surface of BESS infrastructure is extensive and multifaceted. Understanding these vulnerability points is essential for developing effective defensive strategies. The primary attack vector categories include:
- External Perimeter Threats targeting internet-exposed systems and grid interconnection points
- Communication Protocol Vulnerabilities exploiting industrial protocols, particularly Modbus
- Internal System Compromise targeting core operational systems
- Physical and Environmental Access through on-site tampering and manipulation.
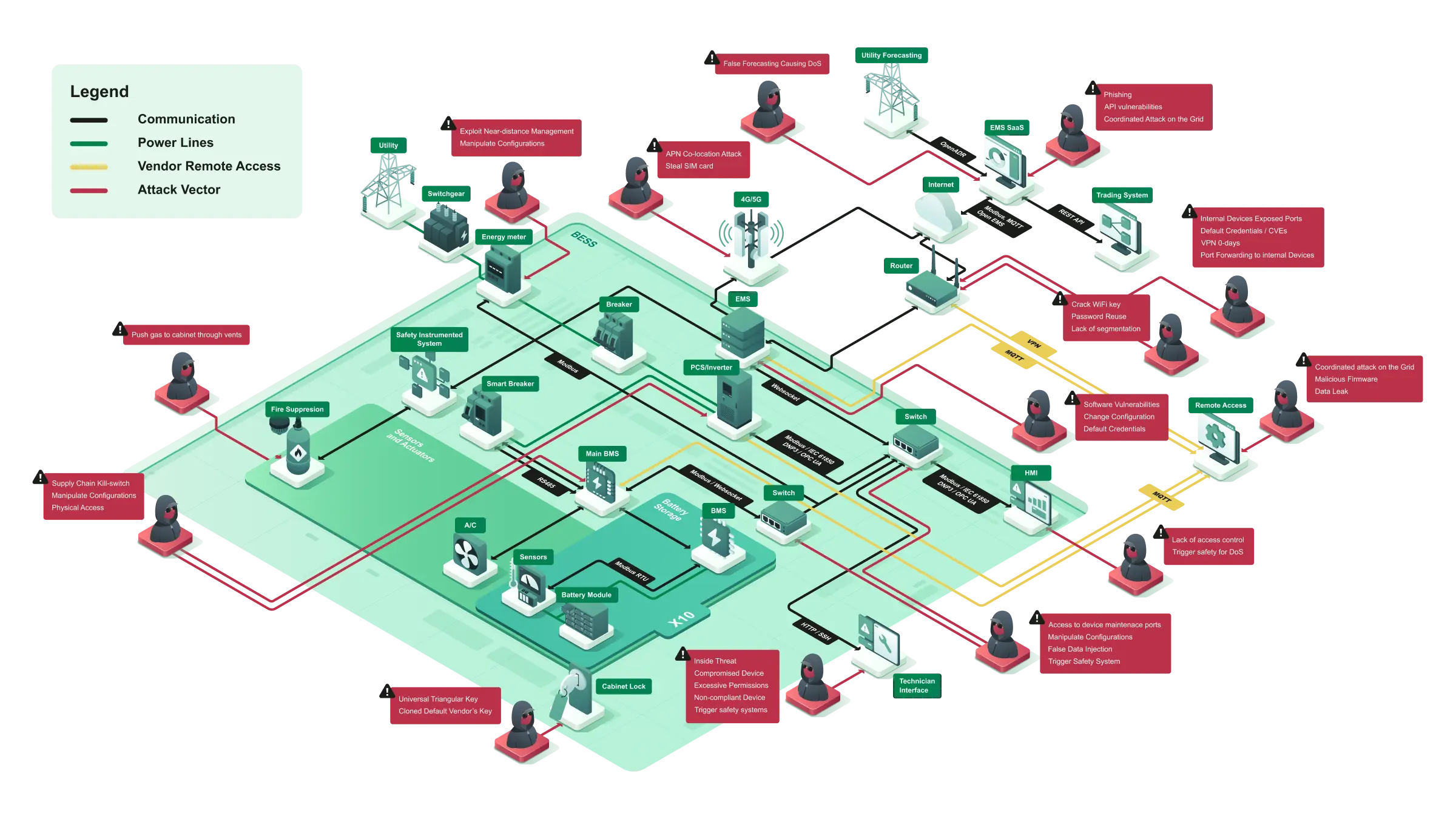
Each category presents unique challenges and requires specialized defensive strategies that traditional IT security approaches cannot adequately address.
Let's examine each category in detail.
1. External Perimeter Threats
The boundary between BESS infrastructure and external networks represents both the first line of defense and the most frequently targeted attack vector.
- The utility interconnection point - where BESS connects to the electrical grid at high voltage, creates opportunities for adversaries to manipulate transformer protection relays, issue unauthorized disconnect commands, or cause cascading grid instabilities. These attacks don't simply affect individual installations; they can prevent BESS from responding during critical grid events, potentially contributing to wider system failures precisely when storage capacity is most needed.
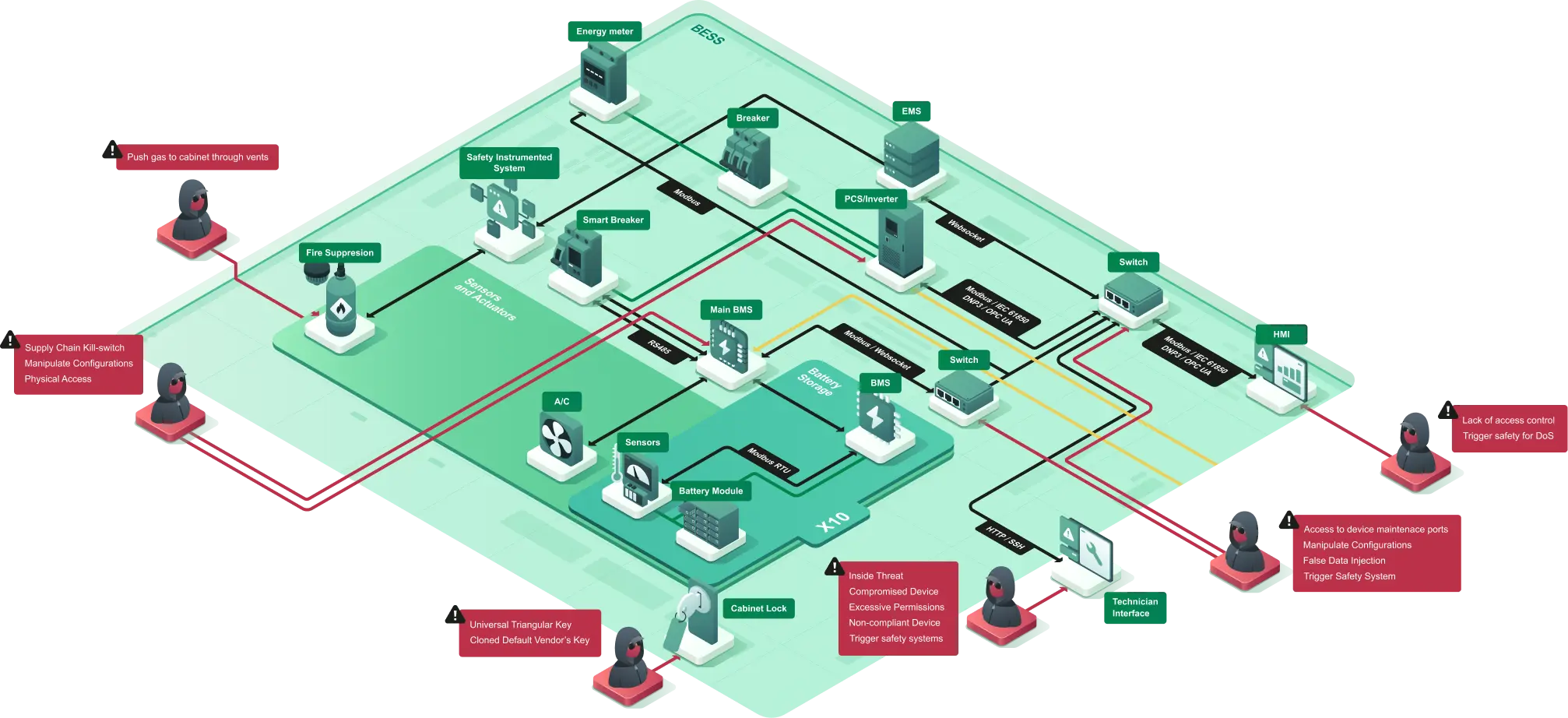
- Internet-exposed systems present another critical vulnerability. Remote Terminal Units (RTUs), Human-Machine Interfaces (HMIs), and remote access gateways provide essential operational capabilities but create direct pathways for adversaries. The above diagram reveals multiple threat actors targeting these internet-facing components, reflecting real-world attack patterns observed across critical infrastructure sectors. These systems often run on legacy platforms with known vulnerabilities, and the operational requirement for remote access creates an inherent tension between security and functionality that CISOs must carefully navigate.
- Supply chain compromise represents perhaps the most insidious threat vector. Malicious firmware or backdoored components embedded during manufacturing bypass perimeter defenses entirely, potentially remaining dormant until activated by adversaries. Battery Management Systems (BMS), inverters, and control hardware from compromised supply chains introduce risks that persist throughout the asset lifecycle. For energy sector CISOs, this threat demands vendor security assessments, hardware verification procedures, and supply chain transparency that extend far beyond traditional procurement practices.
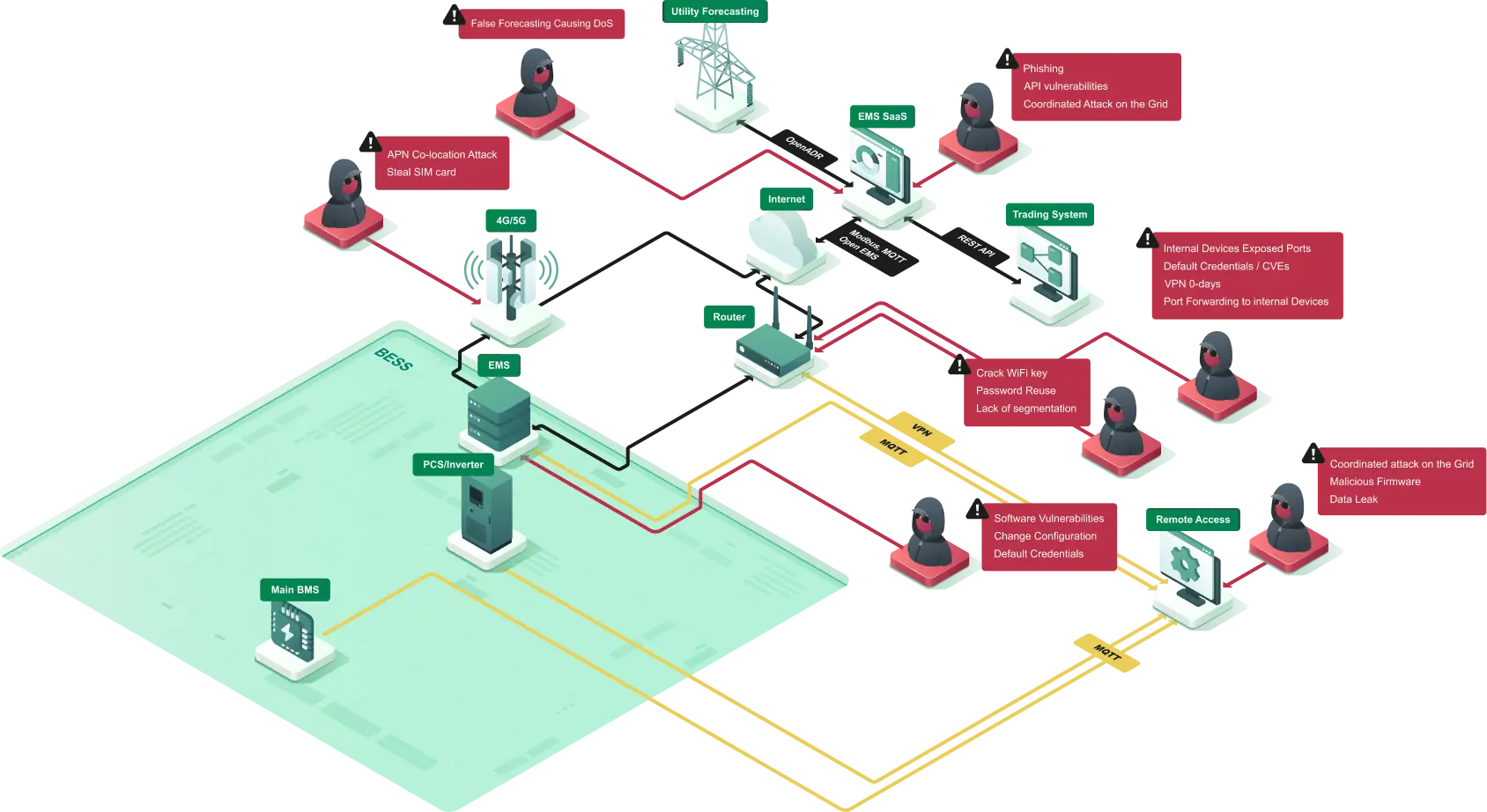
2. Communication Protocol Vulnerabilities
The widespread use of Modbus, particularly Modbus TCP, throughout BESS architecture presents significant security challenges that deserve special attention. Originally designed for isolated industrial networks in an era when cybersecurity was barely considered, Modbus lacks native authentication, encryption, or integrity verification.
For CISOs accustomed to securing enterprise IT systems with robust authentication and encryption standards, the reality of industrial protocols can be jarring. Yet these protocols form the backbone of BESS operations, carrying commands that directly control physical processes and safety systems.
The above diagram illustrates how Modbus connections permeate every level of BESS architecture.
- RTU to BMS communications carry battery state data that inform critical charging and discharging decisions. Adversaries compromising these channels could inject false battery state-of-charge information, triggering inappropriate responses that degrade battery life or create dangerous conditions.
- BMS to main inverter links carry commands that directly control power conversion. Manipulation here could cause physical damage through overcharging, deep discharge, or thermal runaway conditions - scenarios where cyber incidents create immediate physical safety consequences.
- SCADA to field device connections enable system-wide coordination but also provide high-value targets for adversaries. Compromise at this level enables unauthorized control commands while displaying false status information to operators - the classic scenario where technical staff make decisions based on corrupted data, potentially exacerbating rather than mitigating incidents. The lack of encryption in these protocols means adversaries with network access can passively intercept operational data, mapping system behavior and identifying optimal attack timing without triggering any defensive alerts.
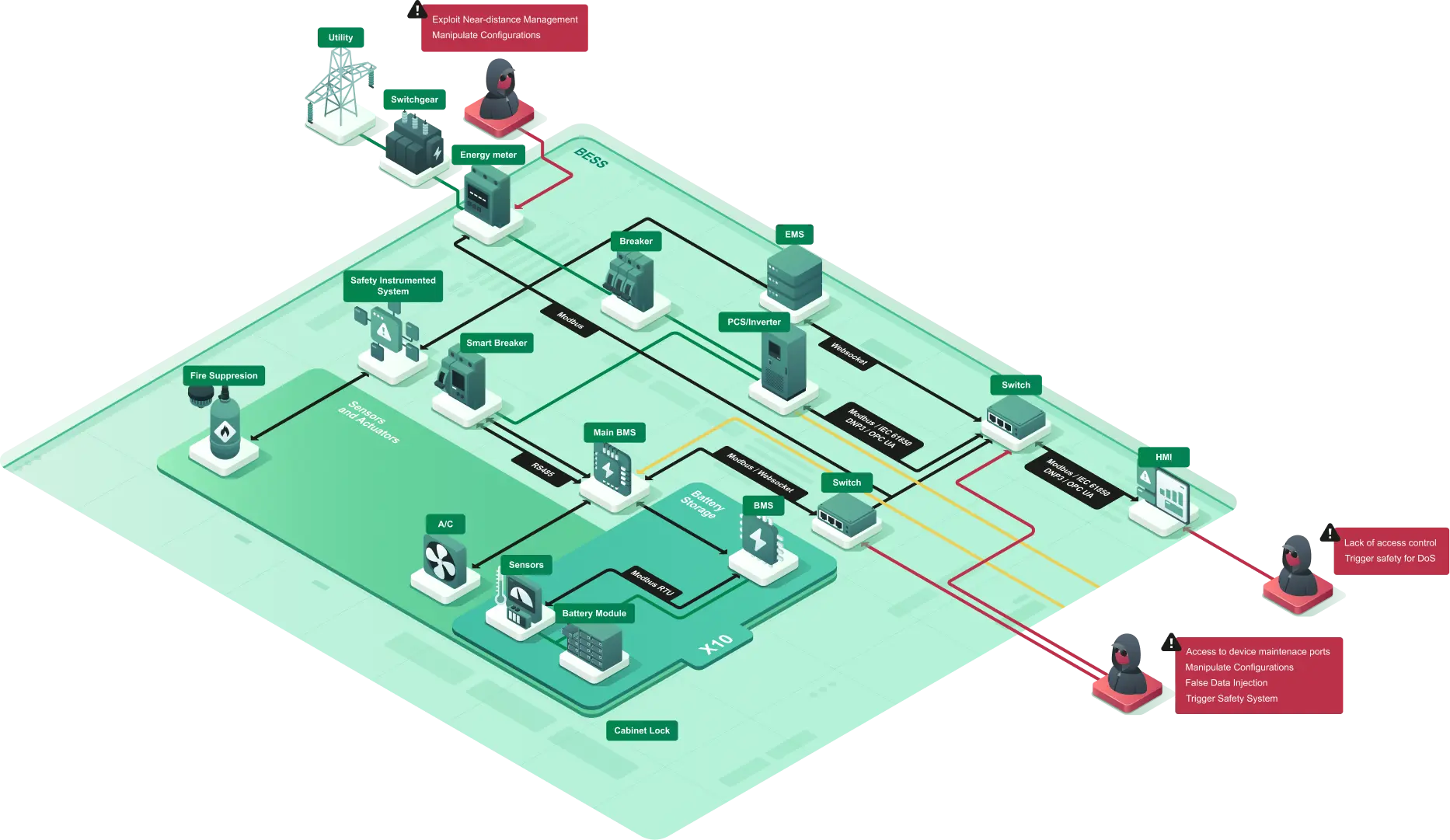
3. Internal System Compromise
Once adversaries breach perimeter defenses, internal systems become high-value targets with extensive control capabilities.
- The Energy Management System (EMS) serves as the central coordination point for BESS operations, making it an attractive target for sophisticated attackers. Successful EMS compromise enables adversaries to manipulate bidding strategies in energy markets, prevent response to grid emergencies, or coordinate attacks across multiple distributed assets. For organizations operating portfolio-wide BESS deployments, a compromised EMS could provide adversaries with system-wide control, turning distributed assets into a coordinated threat vector.
- Fire suppression systems represent a particularly dangerous attack target where cybersecurity directly intersects with physical safety. Adversaries could disable suppression systems before triggering battery thermal events, creating scenarios where cyber and physical attacks combine for maximum impact. Alternatively, false activations could damage sensitive equipment through chemical discharge, creating expensive operational disruptions. For CISOs, this highlights why BESS cybersecurity requires close collaboration with safety engineers and emergency response personnel - traditional security operations center teams may lack the context to properly assess threats to safety systems.
4. Physical and Environmental Access
Physical security remains a critical concern, particularly for distributed BESS installations in remote or less-secure locations.
- On-Site Physical Access - technicians, contractors, and maintenance personnel require legitimate physical access to battery modules, converters, and protection systems. This creates opportunities for insider threats or credential compromise where malicious actors introduce rogue devices, modify system configurations, or install hardware implants for persistent remote access. Unlike centralized facilities with robust physical security, distributed BESS installations may have minimal on-site security, making physical attack vectors particularly relevant to the threat model.
- Component-level tampering presents risks that extend beyond typical physical security concerns. Direct access to Battery Management System hardware, manipulation of AC/DC converter firmware, or modification of sensor calibrations can create persistent compromises that survive software updates and network security improvements.
For CISOs developing security architectures, this demands physical security measures that match the criticality of the assets, including tamper-evident seals, video surveillance, access logging, and regular physical inspections that verify system integrity.
Consequence Scenarios: Beyond Data Breaches
BESS cybersecurity incidents differ fundamentally from typical IT security breaches, a distinction that energy sector CISOs must clearly communicate to boards and executive leadership.
While enterprise security focuses primarily on data confidentiality, integrity, and availability, BESS security encompasses physical safety, grid stability, and market integrity. Understanding these consequence scenarios helps justify security investments and prioritize defensive measures appropriately.
- Physical Damage & Safety Hazards: Lithium-ion batteries operate within narrow safety parameters where cyberattacks can create catastrophic physical consequences. Overcharge conditions can lead to battery cell rupture, with thermal runaway cascading across battery modules. The resulting fires release toxic gases, create explosion risks, and can destroy multi-million dollar facilities while endangering personnel and surrounding communities. These aren't theoretical concerns - the energy sector has witnessed numerous battery fire incidents from operational failures, and adversaries with cyber access could deliberately trigger similar events. For CISOs, this means security failures can result in loss of life, environmental contamination, and liability exposure that far exceeds typical enterprise security incident consequences.
- Grid Destabilization represents another category of consequences unique to energy infrastructure. BESS systems provide critical frequency regulation, voltage support, and emergency response capabilities. Coordinated cyberattacks manipulating these services could trigger cascading failures during peak demand or system stress. Adversaries simultaneously disconnecting multiple distributed BESS installations or causing them to respond inappropriately to grid conditions could contribute to blackouts affecting millions. For CISOs responsible for assets providing essential grid services, security failures don't just impact their organization - they potentially affect entire regions, creating regulatory scrutiny, reputational damage, and public safety concerns.
- Economic Manipulation: financial consequences extend beyond direct operational losses to include market manipulation and regulatory penalties. Adversaries manipulating BESS bidding strategies could profit from artificial price movements while causing financial losses to legitimate operators. Energy markets rely on accurate reporting and rational participation; compromised BESS systems providing false data or behaving unpredictably undermine market integrity. Regulatory investigations following security incidents could result in substantial penalties, loss of market access, and requirements for expensive remediation measures. For CISOs building security business cases, these economic impacts often provide the most tangible metrics for justifying security investments to financial stakeholders.
- Operational Disruption: Even without causing physical damage, cyberattacks that force BESS offline eliminate grid flexibility during critical periods, potentially requiring expensive backup generation or load shedding.
Implementing Energy-Contextual Cybersecurity
Addressing BESS cybersecurity requires moving beyond traditional IT security frameworks toward energy-specific strategies that understand operational constraints, physical consequences, and the unique characteristics of operational technology environments.
Six fundamental pillars support effective BESS security programs:
- Comprehensive Asset Visibility
- Threat Detection with Operational Intelligence
- Proactive Vulnerability Management
- Secure Protocol Implementation
- Defense in Depth Architecture
- Incident Response Planning.
For CISOs, success requires balancing security rigor with operational requirements, leveraging specialized OT security tools, and building teams with both cybersecurity expertise and energy domain knowledge.
1. Comprehensive Asset Visibility
Challenge: Many BESS operators lack complete inventories of connected devices, communication pathways, and software versions across their installations, a visibility gap that creates blind spots where threats develop undetected.
Solution: Deploy continuous asset discovery and network monitoring tailored to energy-operational technology environments. This includes:
- Passive network traffic analysis to identify all communicating devices without disrupting operations.
- Automated detection of unauthorized devices or configuration changes.
- Firmware and software version tracking across all control system components.
- Mapping of communication flows to identify unexpected pathways.
Energy-contextual visibility extends beyond device inventories to understanding operational states-distinguishing between normal operational variations and anomalous behaviors that may indicate compromise.
2. Threat Detection with Energy-Operational Intelligence
Challenge: Traditional cybersecurity tools generate excessive false positives in industrial environments because they lack understanding of operational context and physics-based constraints.
A security alert about unusual Modbus traffic might indicate an attack-or might simply reflect normal operational responses to grid conditions.
For CISOs, this creates a critical challenge: security systems that cry wolf lead to alert fatigue, while systems tuned to reduce false positives risk missing genuine threats.
Solution: Implement threat detection systems with embedded energy domain expertise:
- Protocol-Aware Monitoring: Deep packet inspection of Modbus, DNP3, IEC 61850, and other energy-focused protocols to detect malformed commands, unauthorized function codes, or out-of-sequence operations. This goes beyond simple signature-based detection to understand protocol semantics and operational logic.
- Physics-Based Anomaly Detection: Machine learning models trained on the physical relationships between battery state-of-charge, temperature, current flow, and power output to identify impossible or dangerous operating conditions that violate fundamental energy conservation laws or battery chemistry constraints.
- Behavioral Baselines: Establish normal operational patterns for each BESS installation, accounting for seasonal variations, market participation patterns, and grid service schedules. Effective threat detection understands these nuances, establishing baselines that account for legitimate operational diversity while detecting genuine anomalies
For CISOs, this operational intelligence transforms security monitoring from a source of noise requiring constant analyst attention into a focused capability that highlights scenarios with real physical consequences - commands that could cause overcharge, abnormal thermal conditions, unexpected disconnection requests, or disabled safety systems.
3. Proactive Vulnerability Management
Challenge: Industrial control systems in BESS installations often run outdated software due to concerns about operational disruption, vendor support limitations, and lengthy testing requirements. Operational requirements dictate that systems remain available 24/7, making maintenance windows scarce.
Vendors may release patches slowly or require expensive support contracts for security updates. Some systems run on legacy platforms where patches simply aren't available. Testing requirements are extensive - patches that cause operational disruptions or create safety issues are worse than the vulnerabilities they address.
For CISOs accustomed to rapid enterprise patch cycles, the constraints of OT vulnerability management require different strategies and realistic expectations
Solution: Structured vulnerability management programs designed for operational environments:
- Comprehensive Asset Inventories: Maintain detailed records of all hardware models, firmware versions, and software installations across BESS components.
- Risk-Based Prioritization: Focus remediation efforts on vulnerabilities affecting internet-exposed systems, those with known exploit code, or weaknesses in safety-critical components.
- Vendor Coordination: Establish clear communication channels with equipment manufacturers for security advisories and patch availability.
- Virtual Patching: Deploy network-based compensating controls when direct patching would disrupt operations or void warranties.
- Segmentation Strategies: Isolate high-risk or unpatchable systems through network architecture rather than relying solely on software updates.
4. Secure Protocol Implementation
Challenge: Legacy protocols like Modbus lack security features, yet wholesale replacement is economically and operationally infeasible. New installations may support more secure protocols, but the installed base of Modbus-based systems will persist for decades.
For CISOs, this means security strategies must work with existing protocols rather than requiring their replacement.
Solution: Layer security controls around vulnerable protocols:
- Network Segmentation: Isolate Modbus communications within dedicated VLANs with strict firewall rules limiting access to only necessary communication pairs
- Next-Gen Firewall Contextual Policies: Enforce energy and Modbus-contextual policies, aimed at preventing Modbus malicious function codes from being executed.
- Encrypted Tunnels: Wrap Modbus traffic in VPN or TLS connections when traversing untrusted networks
- One-Way Data Flows: Where possible, implement unidirectional gateways for monitoring data flows to prevent command injection from less-trusted networks
5. Defense in Depth Architecture
Given the multiple attack vectors illustrated in the above diagram, no single security control provides adequate protection. Layered defensive strategies are essential:
Perimeter Security:
- Firewalls with industrial protocol awareness
- Intrusion detection systems tuned for operational technology traffic
- Secure remote access platforms with multi-factor authentication
Network Segmentation:
- Separate VLANs for control networks, safety systems, and business networks
- Micro-segmentation within BESS control networks limiting device-to-device communication
- Isolated management networks for administrative access
Endpoint Hardening:
- Application whitelisting on HMIs and engineering workstations
- Removal of unnecessary services and protocols from control system devices
- Secure configuration baselines for all BESS components
Access Control:
- Role-based access control with principle of least privilege
- Multi-factor authentication for all remote and administrative access
- Physical access controls with logging and monitoring
- Vendor and contractor access management with time-limited credentials
6. Incident Response Planning
Organizations must prepare for the inevitable security incident with response plans that account for both cyber and physical consequences:
- Pre-defined Playbooks: Documented procedures for common attack scenarios (ransomware, unauthorized control commands, compromised credentials).
- Safety-First Protocols: Clear authority for emergency shutdown when cybersecurity incidents create safety risks.
- Stored Logs: Maintain and store data logs in a centralized place, so it would be easy to investigate properly upon an ongoing cyber incident.
- Communication Plans: Coordination procedures with grid operators, equipment vendors, law enforcement, and regulators.
- Evidence Preservation: Procedures for maintaining forensic evidence while prioritizing operational recovery.
- Restoration Procedures: Validated processes for safely returning BESS to service after security incidents.
Regulatory and Industry Initiatives
The energy sector is beginning to address BESS cybersecurity through regulatory frameworks and industry standards, though significant gaps remain.
For CISOs, understanding the regulatory landscape helps ensure compliance while informing security program development.
- NERC CIP standards now apply to larger North American BESS installations, requiring baseline cybersecurity controls, periodic security assessments, and incident reporting. However, many smaller distributed installations fall below regulatory thresholds, creating protection gaps in precisely the distributed assets that contribute most to attack surface expansion.
- IEC 62351 provides international standards for securing power system communication protocols, specifying authentication, encryption, and key management requirements. While technically comprehensive, optional implementation and complex deployment requirements have limited adoption.
- NIST's Cybersecurity Framework offers a risk-based approach adaptable to BESS environments, organizing security programs around five functions: Identify, Protect, Detect, Respond, and Recover. Its flexibility makes it valuable for CISOs developing comprehensive programs, though energy-specific contextualization is essential for effective application.
Significant gaps persist despite these initiatives. Residential BESS systems aggregate into substantial grid resources but lack cybersecurity requirements. International coordination remains inconsistent, complicating multi-national deployments. Regulations struggle to keep pace with rapid technology evolution.
For CISOs, these gaps mean that compliance alone doesn't ensure adequate security - comprehensive security policies must address risks that regulations don't yet cover, anticipating future requirements while managing current threats.
Conclusion: Security as a Strategic Enabler
The cybersecurity challenges facing BESS infrastructure are substantial and growing, but treating security as merely a compliance burden misses the strategic opportunity.
Forward-thinking organizations recognize that robust cybersecurity unlocks tangible business value: better financing terms, expanded market access, reduced insurance premiums, and stronger stakeholder confidence in the energy transition.
As the sector transforms toward distributed, renewable-heavy architectures, security must be foundational from day one.
The BESS attack vector landscape we've explored serves not as a deterrent but as a roadmap - identifying challenges that, when addressed proactively, enable our energy future to be sustainable, resilient, and secure.
Secure Your BESS Infrastructure with SaiFlow
The threats are real. The time to act is now.
SaiFlow specializes in energy-contextual cybersecurity purpose-built for BESS and other distributed energy devices and networks.
We deliver what traditional IT/OT security solutions: deep industrial control system expertise combined with comprehensive understanding of energy sector operations and the physical consequences of security failures.


